Enhanced OAuth security for SSH keys
We just added more granular permissions so third party applications can specifically request read-only access, read/write access, or full admin access to your public SSH keys. You’re in control As…
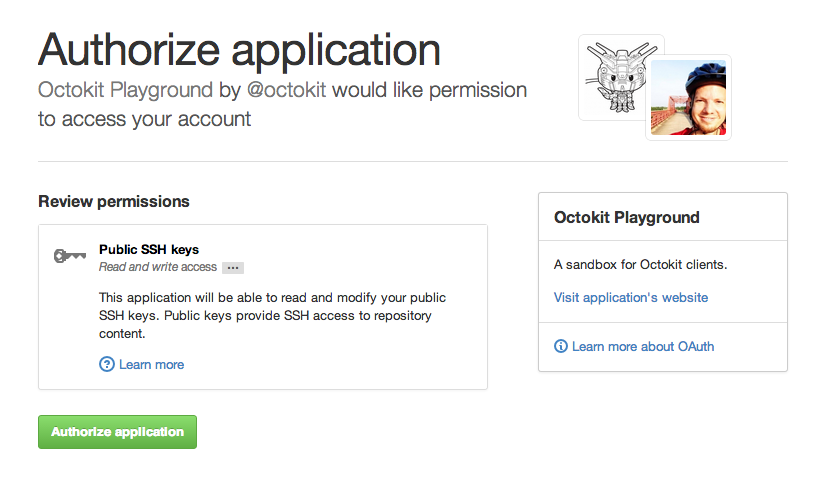
We just added more granular permissions so third party applications can specifically request read-only access, read/write access, or full admin access to your public SSH keys.
You’re in control
As always, when an application requests access to your account, you get to decide whether to grant that access or not.
Revoke with ease
In addition to these finer-grained permissions, we’re also making it easier to revoke SSH access to your data. If an OAuth application creates an SSH key in your account, we’ll automatically delete that key when you revoke the application’s access.
To help you track security events that affect you, we’ll still email you any time a new key is added to your account. And of course, you can audit and delete your SSH keys any time you like.
You can read about the new changes in more detail on the GitHub Developer site.
Tags:
Written by
Related posts

We need a European Sovereign Tech Fund
Open source software is critical infrastructure, but it’s underfunded. With a new feasibility study, GitHub’s developer policy team is building a coalition of policymakers and industry to close the maintenance funding gap.

GitHub Availability Report: June 2025
In June, we experienced three incidents that resulted in degraded performance across GitHub services.

From pair to peer programmer: Our vision for agentic workflows in GitHub Copilot
AI agents in GitHub Copilot don’t just assist developers but actively solve problems through multi-step reasoning and execution. Here’s what that means.